Cybersecurity: The malware that most attacked Android smartphones
ESET points out that old exploits and adapted Trojans continue to dominate the Android ecosystem in Latin America, driven by outdated devices and insecure distribution channels
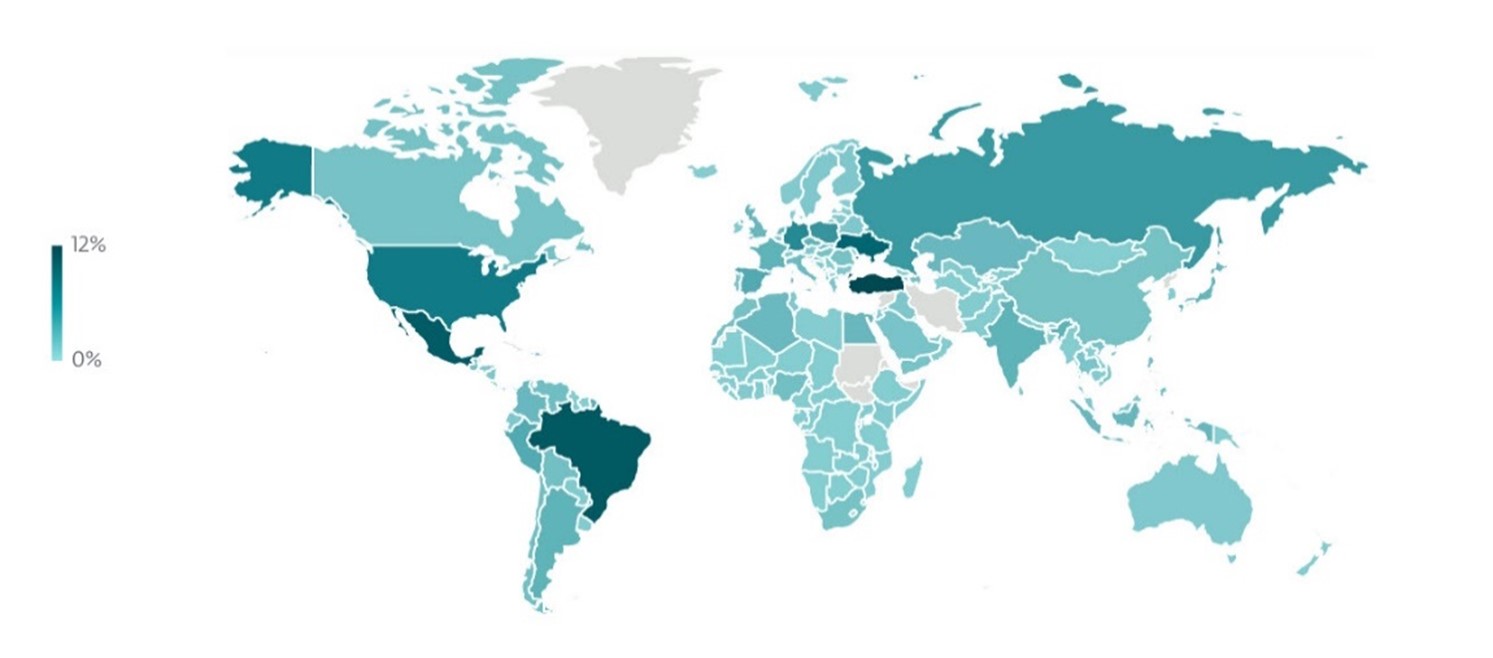
In Latin America, the mobile landscape has very clear characteristics. The region concentrates many malware detections for Android, focusing on Mexico and Brazil, according to the latest ESET Threat Report. Unlike more northerly regions or Europe, Android is the most prevalent operating system by a significant margin. In line with what ESET, a leading company in proactive threat detection, observes globally, the phone is the primary device for most people, and recent devices coexist with models that no longer receive updates. According to the research group, this mix of high dependency, fragmentation, and outdated versions creates an environment where many malicious codes find space to proliferate. This is an issue we should all be aware of, whether we are basic and occasional users or advanced and active ones.
“In addition, many of the most effective distribution channels remain fully operational in the region. SMS or messaging campaigns with direct links, modified APKs shared outside of official stores, and applications that manage to enter legitimate stores with very few reviews or signs of real activity continue to be key vectors. This ecosystem facilitates both the circulation of known malware families and the constant emergence of new or unsophisticated variants that still manage to gain traction,” comments Martina Lopez, Cybersecurity Researcher at ESET Latin America.
ESET analyzes the 3 most frequently detected malware families in the region during 2025
Trojan.Android/Exploit.CVE-2012-6636: An old vulnerability that remains present in the mobile ecosystem because many Android applications continue to use legacy components. The flaw affects apps that use WebView with an insecure configuration and that were compiled with versions prior to Android 4.2. Even if the device is modern, the application may retain this vulnerable behavior. In this context, a malicious webpage loaded within the WebView itself can interact with the app’s internal code in ways that should not be possible, opening the door to the execution of unauthorized actions.
In the current mobile threat landscape, this exploit is not usually the focus of complex campaigns, but it does appear embedded in APKs distributed outside of official app stores or present in applications that no longer receive updates. Publicly available exploits exist for CVE-2012-6636, including modules embedded in frameworks like Metasploit, making it easy for malicious actors to use. Furthermore, it was reported as one of the most prevalent Android exploits in 2023, according to the ESET Security Report 2024.
Trojan.Android/Exploit.Lotoor: This is a family of privilege escalation exploits used for over a decade to gain root access on Android devices. It encompasses a set of techniques that abuse operating system vulnerabilities in various early versions of Android, especially flaws discovered between 2010 and 2013. Under this umbrella are exploits that take advantage of errors in drivers, system services, or memory management, allowing code to be executed with privileges higher than those of the application.
Its modules continue to reappear within malicious tools that seek to activate advanced functions such as uninstalling security apps, modifying internal configurations, or installing additional payloads. This is not the first time the research team has observed Lotoor in the top spots.
Trojan.Android/Pandora: This is malicious code linked to a variant of Mirai adapted for the Android ecosystem. It was first observed in 2023 within popular streaming applications in the region, especially on Android TV boxes and sticks commonly used to access unofficial content. In these cases, attackers distribute APKs that function as legitimate streaming apps but include a malicious component capable of turning the device into part of a botnet. In some models, modified firmware was even detected that came infected from the factory, amplifying the reach of the attack.
Once installed, Pandora maintains communication with a command and control server, receives instructions, and executes the typical capabilities of a Mirai-based botnet, with the focus on launching distributed denial-of-service attacks.

“This 2025 outlook shows us that Android threats continue to rely on well-known vectors and the lack of device and application updates, which keeps exploits and vulnerabilities that have been circulating for years alive. Even so, this doesn’t mean the risk is limited to the usual suspects. Less widespread, but equally relevant, threats also persist, such as banking trojans or fraudulent lending apps, which operate in a much more targeted way and seek a direct impact on the user’s finances. And, in parallel, emerging threats and increasingly innovative techniques are appearing, such as malware capable of cloning cards via NFC, reflecting a constantly evolving mobile ecosystem with a growing level of sophistication,” concludes Lopez from ESET Latin America.
In this context, protecting information and devices from these threats becomes vital.
ESET shares the following tips to avoid becoming a victim
- Keep your device updated and don’t use older versions of Android if an update is available.
- Install applications only from official stores or verified sources.
- Avoid APKs from unknown sources, even if they promise “premium” features or free content.
- Check permissions, developer activity, and the actual number of reviews before installing an app.
- Use reliable security solutions that detect exploits, Trojans, and anomalous behavior.
- Avoid disabling system protections and prevent the installation of unknown apps.
- Be wary of messages, links, or ads that promise quick access, discounts, or special features.
ESET invites you to learn more about cybersecurity by visiting: https://www.welivesecurity.com/es/.
For other useful preventative information, also available in Venezuela: https://www.eset.com/ve/, and on their social media channels @eset_ve. Also on Instagram (@esetla) and Facebook (ESET).
Bitfinance.news
(With information and images provided by ESET and Comstat Rowland)
Visit our news channel on Google News and follow us to get accurate, interesting information and stay up to date with everything. You can also see our daily content on X/Twitter and Instagram